Support ENGINEERING
Technical expertise and profound knowledge for technology related challenges.
Technical expertise and profound knowledge for technology related challenges
As a research company, we are focused on cutting-edge technology projects and provide specialised engineering services for areas such as security requirements, technology roadmaps, IT infrastructure services and technical documentation.
Security Policies and Requirements
We develop and evaluate security policies and requirements for embedded systems and resource constrained software packages.
More
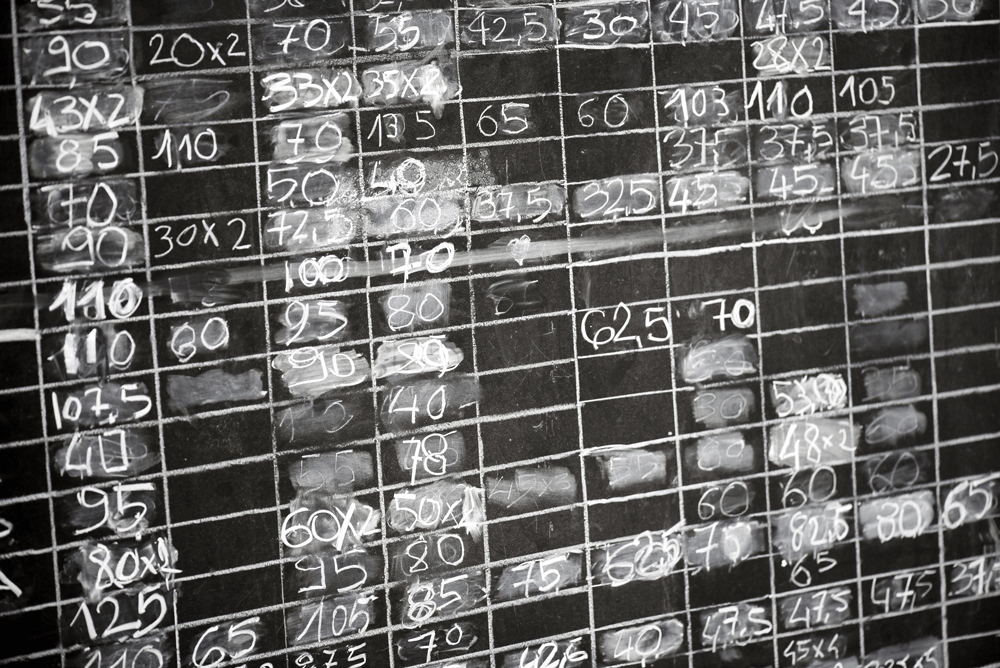
Requirements Engineering
The clear definition, validation and management of requirements and respective use cases is key for all our research topics in various areas. We have profound knowledge and experience in setting-up the requirements engineering process and manage the requirements development continuously.
More
Road Maps and Technology Projection
We research technology roadmaps and perform impact studies. Our work spans from the strategic objectives to the detailed functional individual needs. We strongly consider the given technology and budgetary frame, mitigate risks and adhere to time constraints.
More
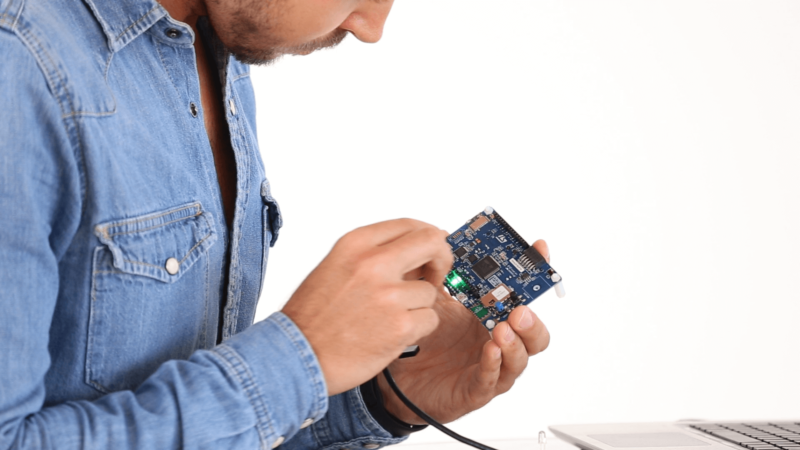
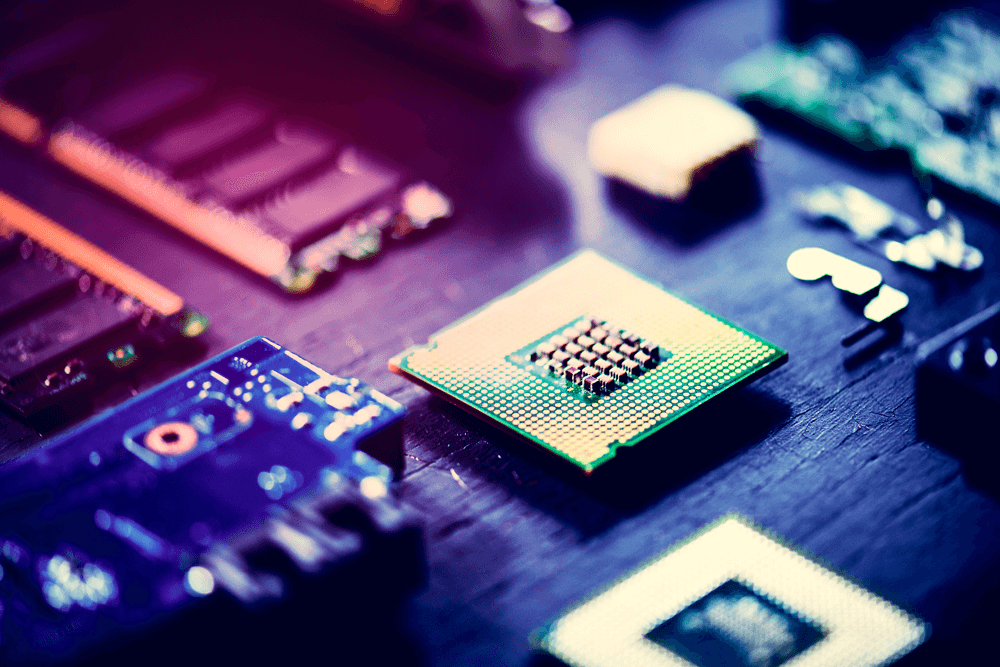
We model, develop and optimize novel security concepts for electronic solutions based on hardware/software entangled security anchors. Among these hardware-based anchors are a variety of architectures with HSM-Modules like TPMs or PUFs. Furthermore, our Root-of-Trust solutions enable a trustworthy authentication of each single edge device by applying a challenge/response principle based on a PUF. Our patented solutions have been integrated in widely available products for secure boot, secure key data storage or secure remote update and upgrade functions.
Our well-defined requirements engineering process includes the requirements specification, verification and validation to produce formal requirement models. All the specifications include functional and non-functional requirements and given constraints for a correct functionality. We are using several tools and methodologies such as data flow diagrams, function decomposition diagrams, V diagrams among others.
Our technology roadmaps allow our customers to strategically address and appraise the future benefits of novel technological solutions. We pave the way for technology rollout by using a defined process including the assessment of the current state, composition of the assumptions and objectives, definition of the strategic technological goals and the development of success metrics.
Our Way to Success

Technical Documentation
It is mandatory that emerging technology and true innovation are accompanied by explanatory material. We design, manage and create professional support material for customers and end users. We provide methods, solutions and support for the documentation of technical systems and products. We are committed to making complex technological products, solutions, relations, or systems understandable. We speak engineering.

Open-Source Platforms and Tools
We develop, maintain and provide various secure collaboration tools to monitor and manage RTD work. These services reside on redundant, high-availability servers in multiple European locations. Our open source collaboration tools serve approximately 3500 concurrent users with single-sign-on functionality. Our IT services based on secure and high-availability virtualised cloud- and on-premise server systems provide the highest level of flexibility due to self-developed features based on our customers’ needs.
References
We have been working for more than 15 years with and for the European Industry and leading Universities. We brought in our engineering work such as security concepts, solutions and benchmark studies to various international research projects and the respective outcome (white papers, deliverables, patents, etc.) has been widely published. We are proud to share our results, here you can find some of our engineering contributions to the research projects funded by the European Commission:
VESSEDIA – Security requirements for connected medium security-critical applications
REINDEER – Use case-driven specifications and technical requirements and initial channel model
REALHOLO – Dissemination report on component and system specification
Showcase

Patented Solutions
We have worked with industry and leading universities for many years in the field of “Physically Unclonable Functions” (PUF). A multitude of international projects have been successfully conducted. We have created security concepts, solutions and benchmarks. Our results have been patented.
Randomness-as-a-Service
Randomness is a critical topic in the cryptographic domain. On most computers, a random number is based mainly on predictable information and the level of randomness is almost zero. As a result, we supply a True-Random-Number-Generator as a service, which is entangled by a PUF, providing a real level of randomness.
Publications / Sharing is caring
We are proud to share our results. A white paper on PUF-based authentication scheme for Internet-of-Thing scenario can be found here:
Research on the Applications of Physically Unclonable Functions within the Internet of Things
A PUF Based Hardware Authentication Scheme for Embedded Devices

Retrofit for security solutions
The steady battle in the field of cybersecurity adds constant pressure for IoT manufacturers. To change the underlying hardware often is very disruptive, especially in cost sensitive areas. Additional costs during the development phase leads in turn to reduction of security levels. At this point in the story, we are coming into the picture. We offer retrofit security solutions for devices already available on the market. We use existing and unexploited hardware features to ramp up your product security.